2018 FLARE-On Challenges Writeup
I decided to participate in this year’s edition of FLARE-On challenge. It is made by the fine folks from FireEye Labs Advanced Reverse Engineering (FLARE) team.
I wanted to see how far I could go. I did not set any goals nor did I took it as seriously as I would have liked.
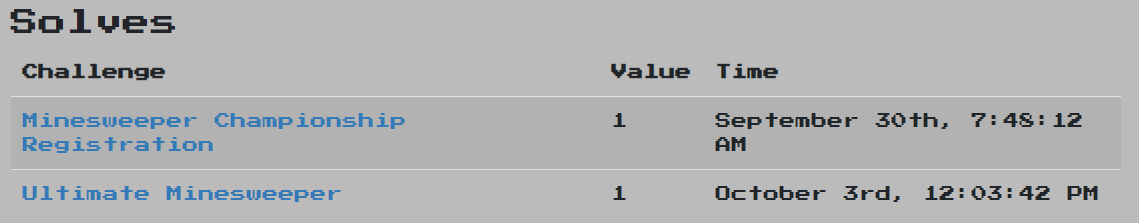
The challenge is now over and I only managed to make it to the 2 challenge, as expected (you can see the reason why above 😆 ). Let’s get on with the challenges.
Minesweeper Championship Registration
Simple challenge. Once you open the zipped file, you’ll get a jar file.
These days I mostly use Bytecode Viewer when it comes to APK or jar files.
Once you open the challenge jar file with it and navigate to the only class file in there you’ll see the following code:
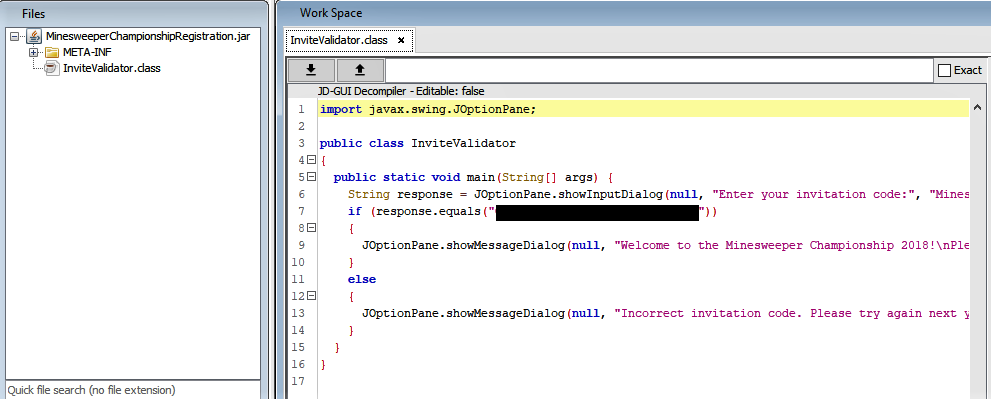
Rest is history! 😉
Ultimate Minesweeper
Boy, was I in for a challenge with this one. 😅
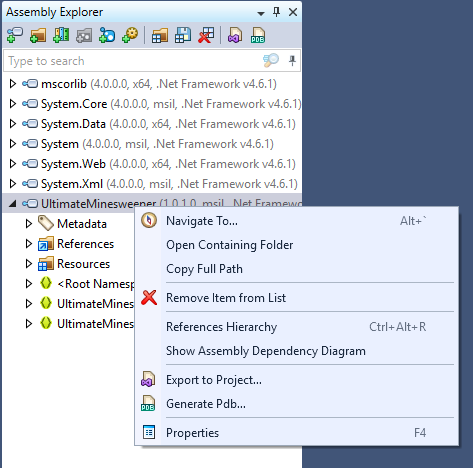
Figured out it was a .NET binary and remembered a friend of mine talking about their experience decompiling them a few months back, I took this opportunity to try it out.
There might have been an easier way than what I will be describing below:
- Opened up the binary using Jetbrains’s dotPeek.
- Exported it to a Visual Studio project.
- Opened up the solution/project with Visual Studio.
- Started looking into the main class.
- Found a function
SquareRevealedCallbackthat is used as a callback after each click on the minefield tiles.
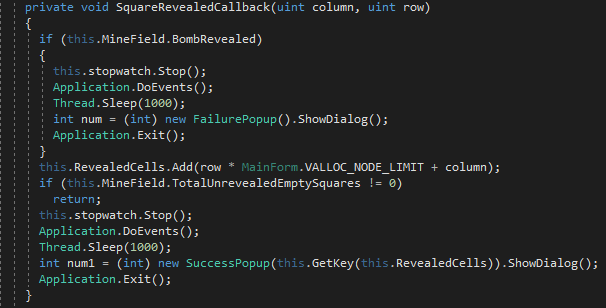
- Got to another function
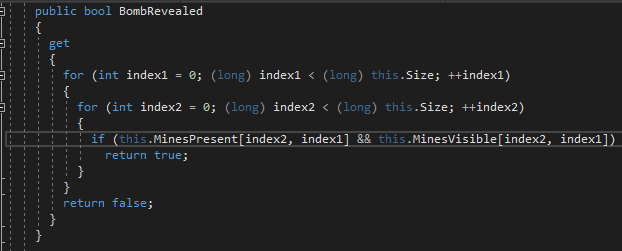
BombRevealedthat checks if any minefields were revealed, which returnstrueorfalseto the callback function above.
- Modified the
ifstatement inBombRevealedas below and rest is some clicking. 😆
if (!this.MinesPresent[index2, index1])
{
System.Console.WriteLine(index1 + 1);
System.Console.WriteLine(index2 + 1);
}

Definitely going to hone my skills before next year’s FLARE-on challenge! 💪 😎
Also check out a more in-depth thorough writeup of the challenges from the authors: https://www.fireeye.com/blog/threat-research/2018/10/2018-flare-on-challenge-solutions.html